European Cybersecurity Companies
Estonia became Europe's de facto centre for military cyber after hosting NATO's Cooperative Cyber Defence Centre of Excellence since 2008, and the country's model of embedding private companies into national cyber resilience has been replicated across the Baltics. The EU committed €1 billion to cyber defence programmes through the European Defence Fund's 2024-2025 work programme, with Germany, France and the Netherlands absorbing the largest contract volumes. Most roles in the sector require national security vetting, making local hiring in high-trust jurisdictions like Tallinn, Helsinki and The Hague the dominant pattern.
Where these companies are based
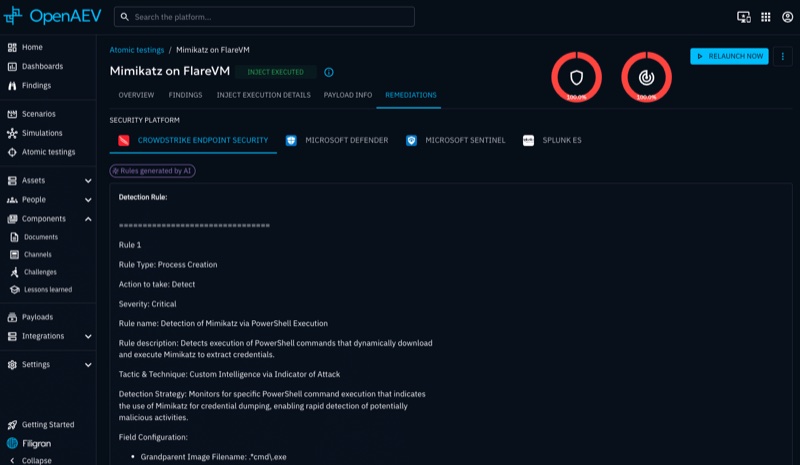
Open-source cyber threat intelligence and adversarial exposure validation platforms used by 6,000+ organisations worldwide, from national intelligence agencies to global enterprises.

Provides offensive and defensive cybersecurity services and software protection tools for software manufacturers, government agencies and defence organisations.
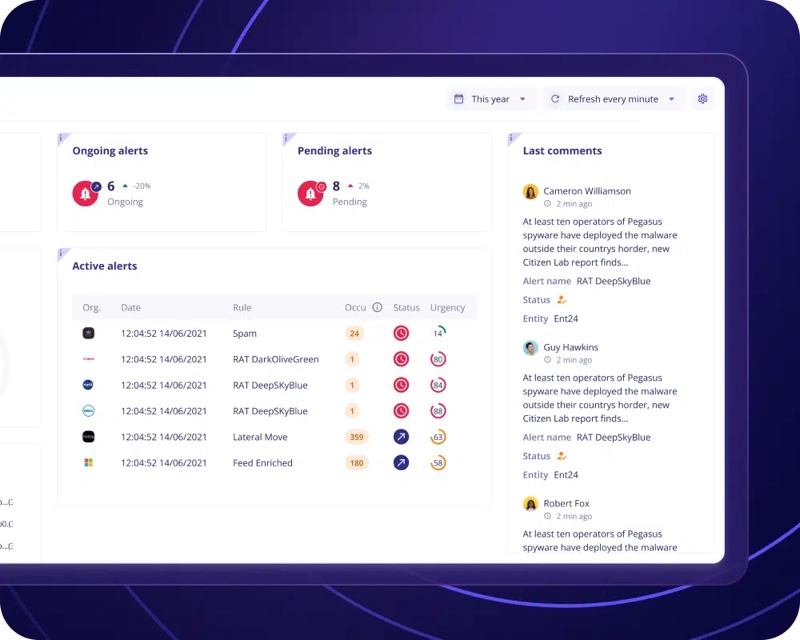
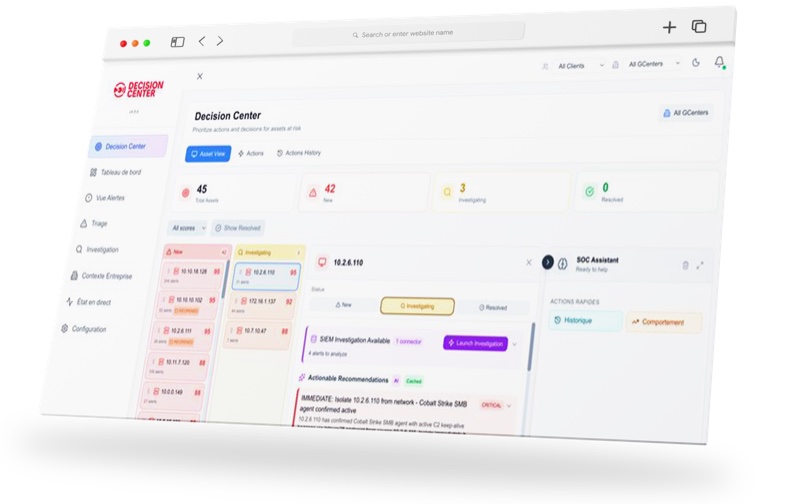
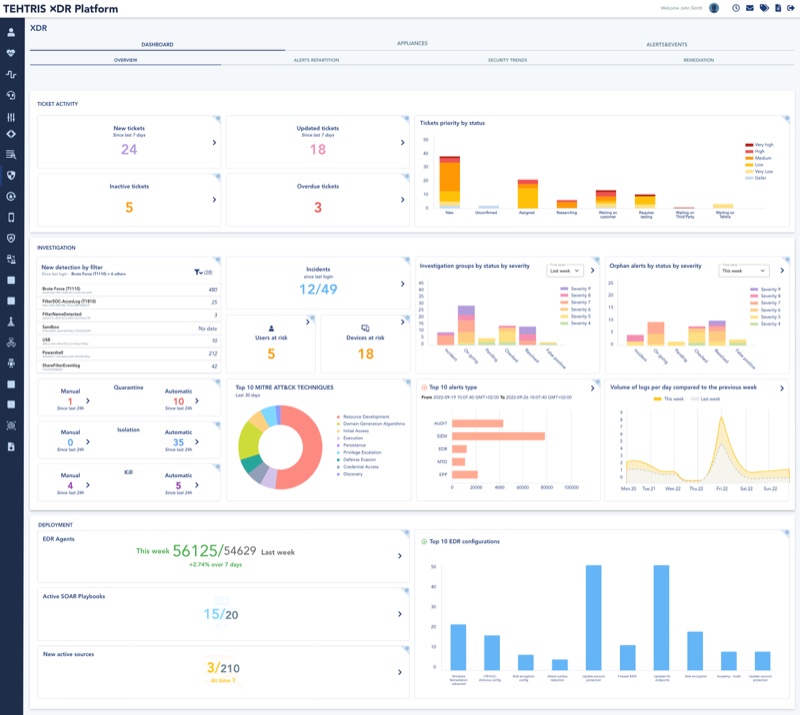
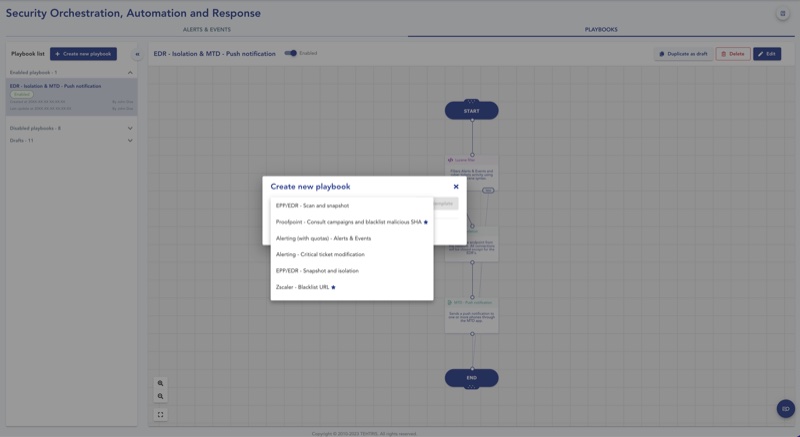
Builds a SOC platform combining extended detection and response (XDR) with cyber threat intelligence for European enterprises and government organisations.
Develops network firewalls, endpoint protection and data encryption products for European defence, government and critical infrastructure organisations, as a subsidiary of Airbus CyberSecurity.



Builds secure data exchange platforms, digital identity systems and maritime surveillance infrastructure for governments in 40+ countries, with roots in creating the technology behind e-Estonia.
Designs memory-safe semiconductors with post-quantum cryptography for securing servers, edge devices and critical infrastructure against both current and quantum-era threats.
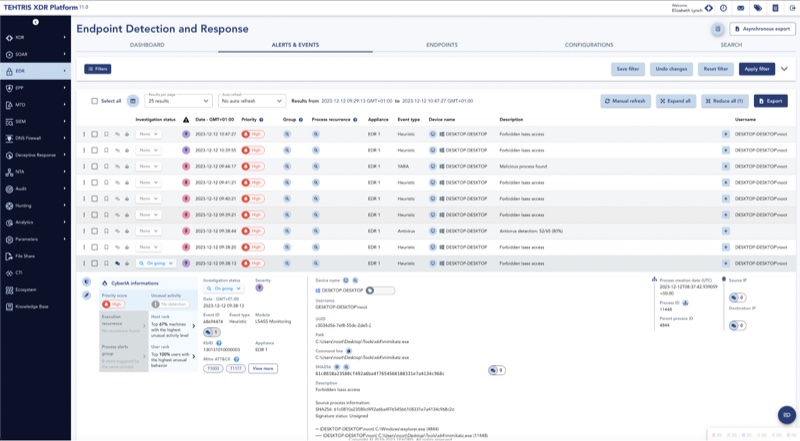
Builds endpoint detection and response software for European enterprises and government agencies, with cloud and on-premises deployment options certified by ANSSI and the German BSI.
Manufacturer of professional wireless security systems providing intrusion protection, fire detection, video surveillance, and automation solutions. Develops advanced security technologies for critical infrastructure protection and defence applications.
Builds OSINT-powered threat intelligence and disinformation detection platforms for governments, security agencies and enterprises.
Builds post-quantum cryptography software that helps governments, financial institutions and critical infrastructure operators inventory their cryptographic assets and migrate to quantum-resistant encryption.
Develops AI-powered video analytics software that transforms video feeds into actionable intelligence for cities, homeland security forces, and businesses, with focus on European sovereignty and GDPR compliance.
Federated learning platform provider enabling secure, privacy-preserving machine learning across distributed data sources without centralizing sensitive data, supporting edge AI deployment in mission-critical environments.
Czech semiconductor company developing auditable, tamper-resistant secure elements for IoT devices, digital identity, and critical infrastructure protection.
AI-powered cybersecurity platform protecting businesses from malicious bot traffic, scrapers, and automated attacks. Rebranded from BotGuard. EUR45M Series B led by Dawn Capital.
Cybsafe is an adaptive Human Risk Management platform that helps security teams reduce risky behaviors at scale. The GCHQ-accredited software delivers behavioral cybersecurity using science-backed approaches, powered by SebDB - the world's security behavior database.
Integrated risk management and analytics company focused on managing digital vulnerabilities inherent in third-party ecosystems. CyDesk platform uses AI and machine learning to automatically evaluate risks from over 900 data sources for cybersecurity, compliance, and business risk management.
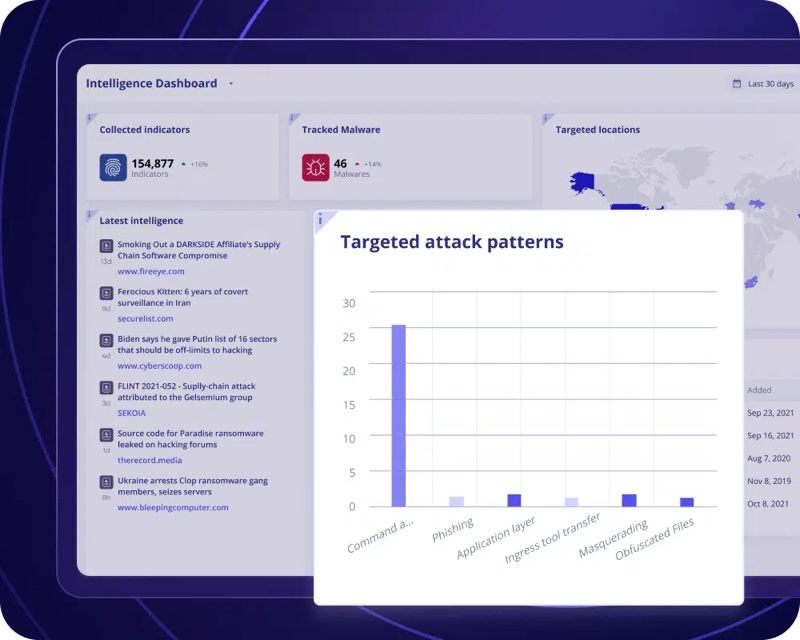
Builds threat intelligence platforms and tools that help security teams collect, process and act on cyber threat data across government, military and enterprise environments.
Automated AI red teaming and security testing. First company to apply dynamic application security testing methodology to AI systems.
AI-powered narrative intelligence platform that tracks disinformation and influence operations across text, broadcast and video media. Deployed by NATO Strategic Communications Centre of Excellence. Raised EUR 2M seed in December 2025.
Builds quantum random number generators and randomness processing units that give encryption systems a hardware-verified source of entropy, covering embedded chipsets through to cloud-scale computing.
UK leader in AI safety, security, and assurance providing testing, evaluation, and monitoring of AI systems. Works with UK Government's AI Safety Institute and Ministry of Defence to identify AI vulnerabilities and enable safe AI deployment in critical defence environments.
Provides automated security data curation pipeline for cybersecurity applications. Their platform helps enterprises achieve high-quality security data through automated collection, transformation and routing, enabling faster threat detection and response.
Predictive attack intelligence using behavioral AI. Advanced threat detection and prevention for critical infrastructure protection.
Private defence research institute specialising in AI, cybersecurity, military UX and IC component design for radar and electronic warfare. Coordinates the EUR 9.7M EDF-funded CYBER4DE project and participates in eight European Defence Fund programmes.
Darknet monitoring and leaked credential detection platform for defence and critical infrastructure. Indexes 80 billion accounts and 300 billion assets with AI-driven risk prioritization. DefenseTech-Inkubator.NRW member.
R&D company building AI, computer vision and cybersecurity tools for defence and space, cleared to NATO SECRET and EU SECRET. Active in EDF projects across multiple EU countries.
Builds a cyber range platform for military, critical infrastructure and enterprise cybersecurity training. Won NATO NCI Agency's Innovation Challenge as best cyber-defence training solution, with 250+ hours of automated attack scenarios.
Provides deception-powered threat intelligence solutions for active cyber defence. Creates controlled, deceptive environments that mimic organizational infrastructure to lure attackers away from real assets while gathering comprehensive threat intelligence.
Open-source collaborative cybersecurity engine using crowd-sourced threat intelligence to block malicious activity in real time.
Provides comprehensive cyber security training solutions to increase organizational cyber resilience through advanced cyber range technology. NATO-awarded Estonian company offers highly realistic live-fire exercises that simulate real-world cyber attacks.
Graph and AI investigation platform that fuses siloed data into a unified knowledge graph, used by defence agencies, national intelligence services and financial institutions to uncover hidden networks and conduct complex investigations.
Manufactures military-grade digital communication systems and field telephone exchanges for the Polish Armed Forces since 1991. Systems have been deployed on Polish military missions in Afghanistan, Iraq, Kosovo and other theatres.
Italian industrial group providing end-to-end IoT and cybersecurity solutions for critical infrastructure, defence, and public administration sectors.


Multi-use technology company developing closed-source intelligence systems and threat detection platforms, focusing on OSINT capabilities and situational awareness solutions.
Develops Energy Logserver, a SIEM and log management platform used by critical infrastructure operators, banks and government institutions. Combines SIEM, EDR, UEBA and network traffic analysis for defence and public sector cybersecurity.
Factiverse develops AI tools for countering harmful narratives and information threats, relevant to national security and information integrity. The company's AI detects false information by analyzing vast amounts of data, evaluating source credibility, and highlighting misinformation networks in 114 languages.
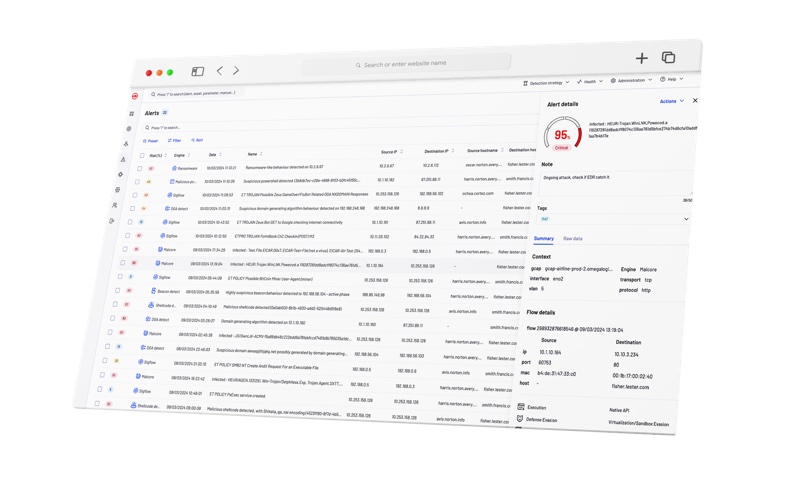
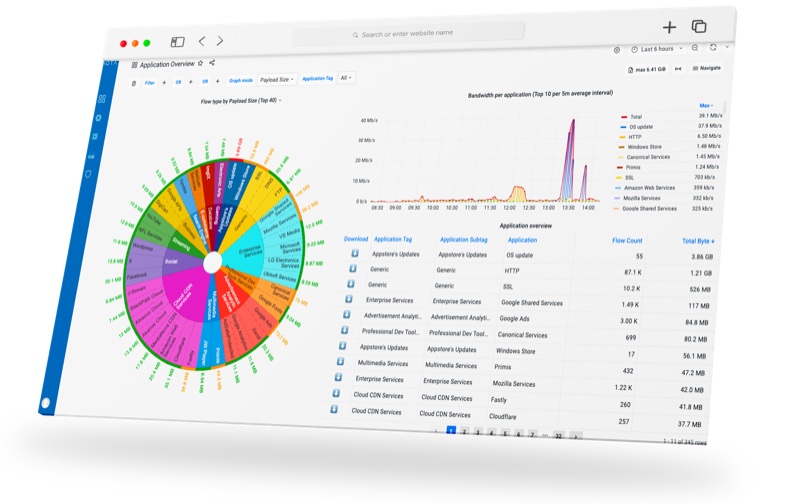
Network detection and response platform providing deep packet inspection for military networks and critical national infrastructure.
AI-powered malware analysis and cyber threat detection platform specializing in rapid automated binary analysis.
Cybersecurity company that provides physical network disconnection technology through the FireBreak platform, enabling remote control of network connectivity without using the internet for ultimate protection against cyber threats.
Builds end-to-end encrypted mobile phones with 4096-bit key exchange and hardened OS. Pioneered the secure smartphone market in 2003 with patented Baseband Firewall that detects IMSI catchers. Used in 50+ countries.
Blockchain-based cybersecurity infrastructure securing military, government, and ESA space systems with keyless signature technology.
First Polish manufacturer of cybersecurity products for industrial control systems. Developed SCADvance XP, a passive IDS for OT networks using deep packet inspection across 70+ industrial protocols.
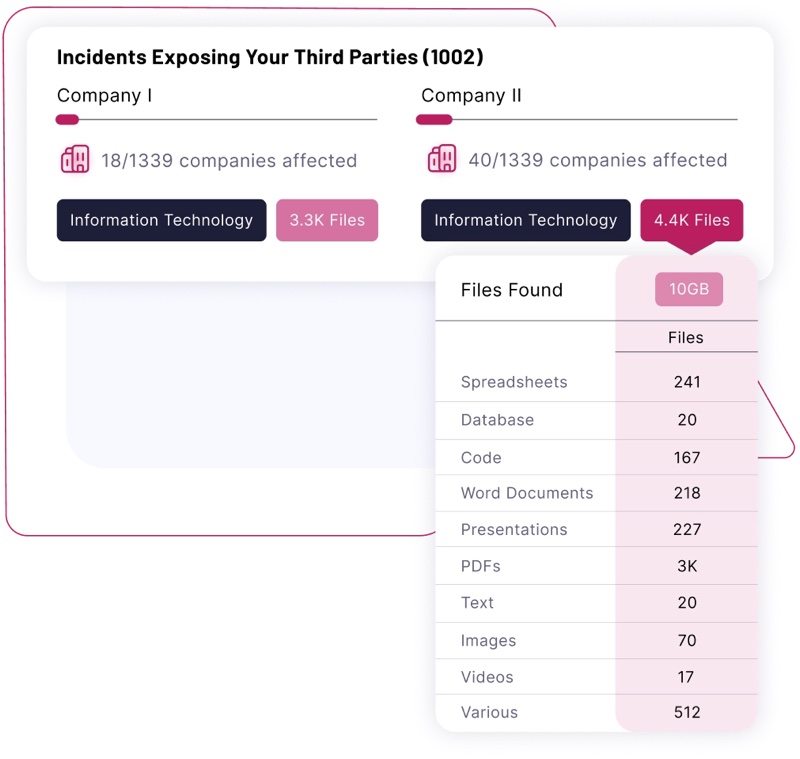
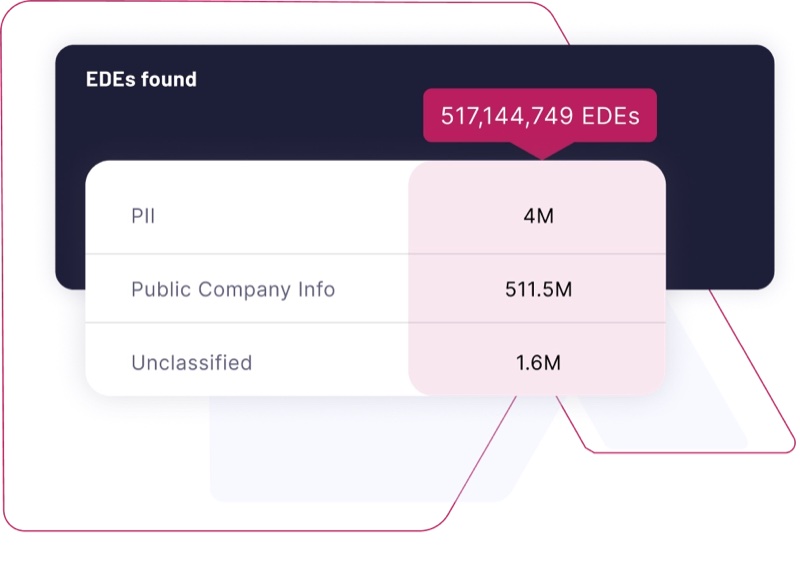
Leading exposed data intelligence platform with Gen AI Agents for threat detection that continuously monitors for exposed data and provides high fidelity intelligence for cybersecurity risk management.
Provides offline data transfer solutions enabling secure data exchange without internet connectivity. Specializes in air-gapped data transfer systems for sensitive environments.
Builds OSINT and link analysis tools that help intelligence agencies, law enforcement and corporate investigators uncover hidden connections across open-source, dark web and commercial data sources.
Provides military TETRA radio systems, electronic warfare equipment and cybersecurity tools to the Polish Armed Forces since 1990. Built the first military TETRA network in Poland.
Cybersecurity company building national-scale SOCs, CSIRTs and threat intelligence platforms. Developed Lithuania's national cyber security strategy alongside the Ministry of Defence. Operates across multiple countries.
Defence security integrator holding NATO and EU classified information clearances. Provides perimeter security with radar, thermal imaging, CCTV analytics and counter-drone systems for military facilities and critical infrastructure across Poland.
Mobile security platform protecting enterprise and defence mobile device fleets against advanced mobile threats and data leakage.
Develops quantum key distribution (QKD) technology providing ultra-secure data communications and quantum networking solutions for critical infrastructure.
Award-winning quantum technology spinout from Oxford University developing quantum random number generators (QRNGs) that provide verifiably secure random numbers for cybersecurity applications.
Deep-tech cybersecurity company focused on hardware implementation of post-quantum cryptography standards. Their secure element chiplet integrates NIST-selected PQC algorithms at the silicon level.
Specializes in Multi-Party Computation technology enabling secure collaboration on encrypted data, allowing organizations to analyze sensitive datasets without exposing raw data.
Cybersecurity company building a User Access Security Broker that deploys multi-factor authentication and passwordless login across enterprise applications without code changes. Trusted by BNP Paribas Bank Polska and major Central European insurers.
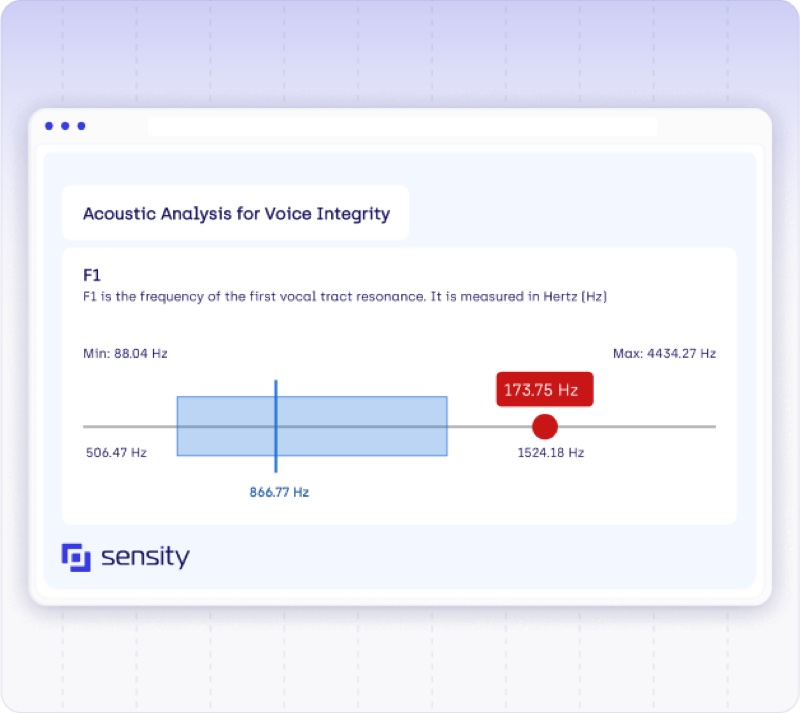
AI-powered deepfake detection platform that identifies synthetic media and provides cybersecurity solutions against AI-generated threats.

Provides OT, ICS and IoT cybersecurity services to industrial and critical infrastructure organisations, covering security audits, penetration testing, red team operations and NIS2 compliance.
Provides an investigative intelligence platform that enables organizations to search, analyze, and visualize data for law enforcement, cybersecurity, fraud, and national security investigations.

Hardware Security Modules and encryption technologies. Advanced cryptographic solutions for defence communications.
European cybersecurity startup specializing in internet invisibility technology through their VIPN (Virtual & Invisible Private Network) system, making users, devices, and data invisible to prevent cyber attacks.
Develops quantum computing hardware and secure access platforms for military IT applications. Part of the PLN 56 million MIKOK consortium building modular quantum computer infrastructure for the Polish Armed Forces under NCRD funding.
Develops cloud-based satellite mission control software (MCSaaS) and operates a Space Cyber Range for space cybersecurity training. Spin-off of ESTCube-1, Estonia's first satellite mission. Prime contractor for ESA 4S Space Cyber Range and participant in NATO CCDCOE Locked Shields exercises.
Extended detection and response (XDR) cybersecurity platform protecting enterprise and defence endpoints against advanced threats.
Designs and manufactures tactical radio relay systems, UAV data links and command-and-control communications equipment for the Polish Armed Forces and NATO air defence programmes.
Secure collaborative analytics platform enabling privacy-preserving computation on sensitive defence and intelligence data. EPFL spinoff.
Provides security-cleared IT consultants and cyber defence tools to NATO, EU agencies and Europol. Operates the CDeX cyber-range exercise platform as a national asset.
Poland's largest private defence company building C4ISR systems, tactical communications and reconnaissance drones. Products include the FlyEye ISR drone and Warmate loitering munition.
